Security Portal
- CISO MessageJump to the applicable section
- PolicyJump to the applicable section
- Information Security Management FrameworkJump to the applicable section
- Information Security GovernanceJump to the applicable section
- Measures for Enhancing SecurityJump to the applicable section
- Cybersecurity Annual ReportJump to the applicable section
- External Security EvaluationJump to the applicable section
- NoticeJump to the applicable section
CISO Message

Senior Managing Executive Officer,
CTO, Executive Director, Core Technology Sector and
Chairperson of the Information Security Subcommittee,
KDDI CORPORATION
As KDDI VISION 2030, KDDI delivers the message, "The creation of a society in which anyone can make their dreams a reality, by enhancing the power to connect," and is engaged in a diverse range of businesses to develop a truly connected society. Information security is a key issue in advancing these initiatives. As a telecommunications carrier that plays a role in core social infrastructure, KDDI positions information security as a critically important issue in order to provide customers with safe and secure telecommunications services at all times.
In recent years, telecommunications have become deeply integrated into all industries and people's daily lives, and with the further integration of AI, their role as social infrastructure has become even more significant. At the same time, cyberattacks have grown increasingly sophisticated and complex. For example, advanced cyberattacks driven by geopolitical factors, including the leakage of confidential information and ransomware attacks, pose serious threats not only to companies but also to national security. In addition, phishing scams continue to increase, leading to damage caused by the unauthorized use of services used by customers.
Under these circumstances, KDDI has established systems to address cyber threats such as unauthorized access to systems, DDoS attacks, ransomware attacks, and damage caused by phishing scams. In addition to initiatives aimed at preventing incidents before they occur, we have built mechanisms to promptly detect and monitor cyberattacks. Furthermore, we are continuously strengthening our security measures by leveraging AI in cyberattack monitoring and other security operations, thereby minimizing the impact of cyberattacks on our services and providing customers with peace of mind. Through these initiatives, we strive to minimize damage to our services caused by cyberattacks and to ensure that our customers can use our telecommunications services with peace of mind.
To protect our customers' critical information assets and telecommunications services, KDDI will continue to evolve its responses to new and emerging threats, and will remain committed to providing safe, secure, and reliable services.
Policy
Policies on Information Security
To address increasingly sophisticated and complex cyberattacks, the KDDI Group recognizes information security risk management as a critically important issue and is committed to strengthening its information security governance.
Specifically, we are establishing the information security management framework, implementing information security measures, and developing internal regulations. These are part of the Security Policy, which establishes the basic policy for information security.
We have established the "KDDI Group Information Security Standards" for our group companies and have implemented them across all KDDI Group companies. Through these standards, we aim to enhance the overall security level of the KDDI Group. In addition, by conducting regular audits, we monitor the security status of each company and continue to strengthen information security governance across the entire KDDI Group.
Basic Policy for Data Utilization and Privacy Policy
KDDI may obtain and use our customers' personal data to contribute to improving their experience and to the sustainable development of society through our business activities, which include the provision of various services and products. The term "personal data" here encompasses not only personal information as defined by the Act on the Protection of Personal Information (hereinafter referred to as the Personal Information Protection Act) but also includes data pertaining to individuals.
In recognition of the importance of personal data, KDDI has established the Basic Policy for Data Utilization as clear guiding principles for our course of action to ensure the protection of personal data. Furthermore, based on this Basic Policy for Data Utilization, KDDI establishes the KDDI Privacy Policy as guidelines for handling personal data. We have established an internal body dedicated to this purpose, have a third party assess our handling of the information, have adopted a privacy impact assessment (PIA) conducted before a service is introduced, and take other actions in order to further ensure that we properly handle customer information.
Information Security Management Framework
KDDI has established the Information Security Subcommittee under the Risk Management Committee, which is chaired by President, Representative Director, to ensure unified information security across the KDDI Group with respect to information assets. This organization-wide framework enables KDDI to accurately understand the status of information security management and to swiftly deploy various measures to strengthen information security throughout the entire Group.
The Risk Management Committee serves as the central body overseeing risk management and consists of seven subcommittees, including the Information Security Subcommittee. Through this structure, KDDI centrally consolidates significant management risks and promptly implements necessary measures based on risk analysis.
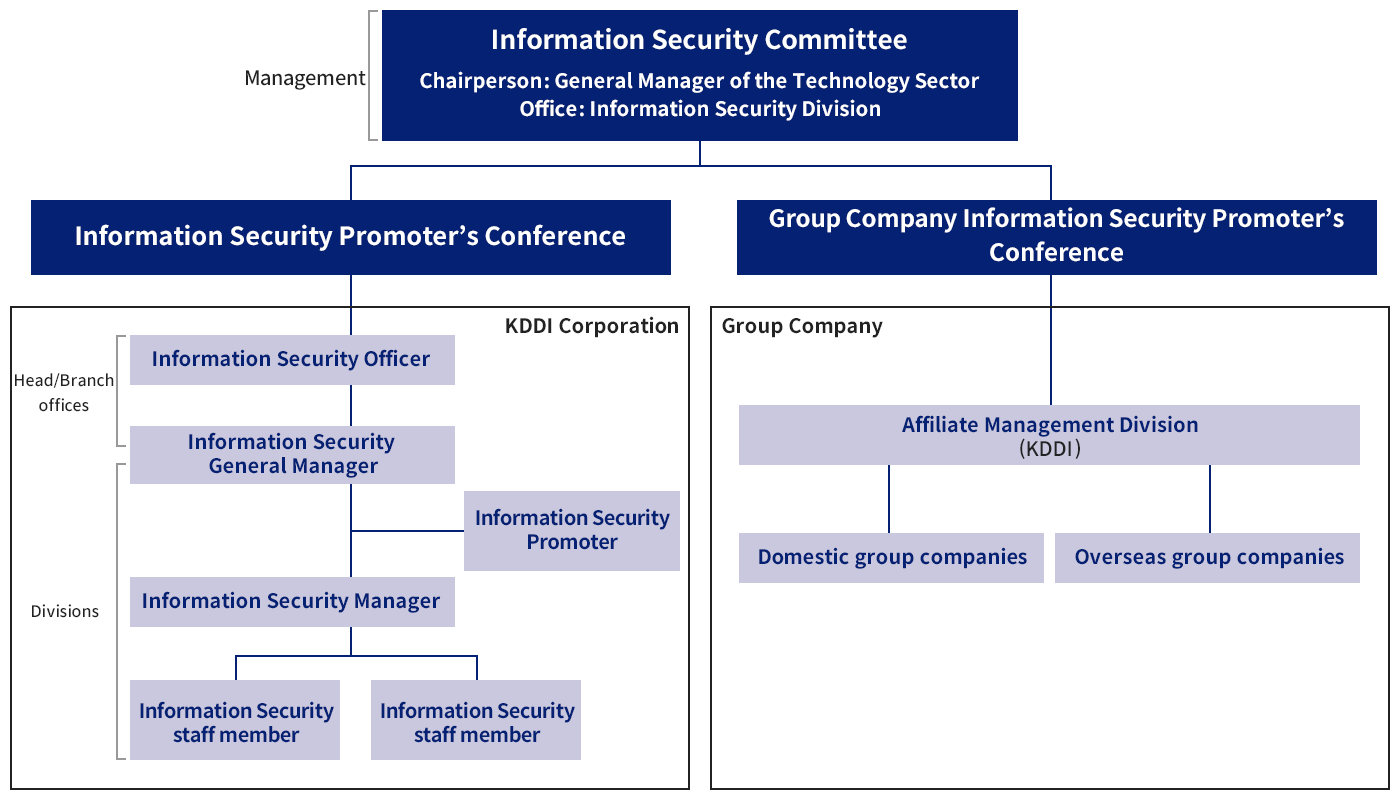
Information Security Subcommittee
To ensure unified information security across KDDI and the entire KDDI Group, we have established the Information Security Subcommittee, composed of members from the management level and heads of the Sales, Technology, and Corporate divisions. This subcommittee is designed to build a company-wide organizational framework to maintain unified information security over information assets. Under the Information Security Subcommittee, we have also established the Information Security Promoters' Conference and the Group Company Information Security Promoters' Conference, composed of representatives from each division within KDDI and its Group companies. This structure enables the establishment of an information security promotion system throughout the entire KDDI Group.
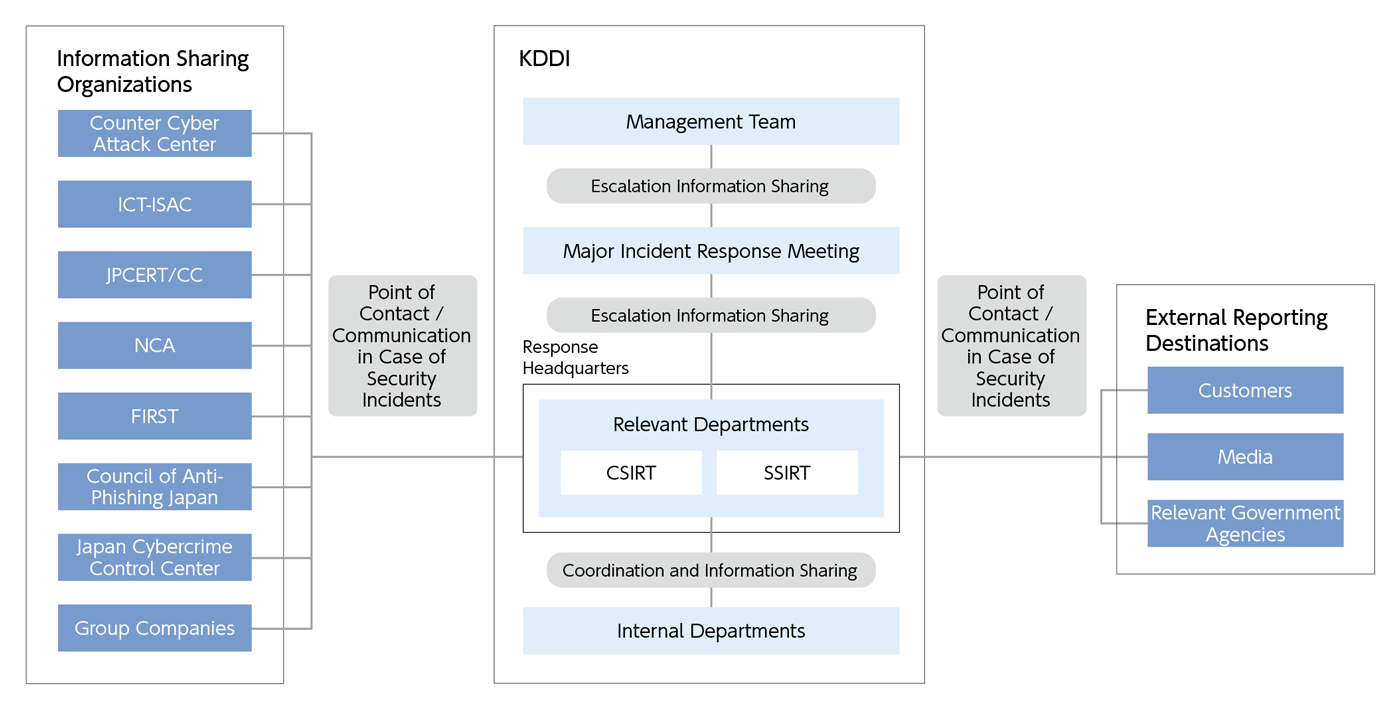
Security Incident Response Framework
KDDI has established and operates a reporting system that enables employees to respond quickly and appropriately when they discover security incidents, vulnerabilities, or suspicious activities. In the event of a security incident such as an information leak, relevant departments of the Response Headquarters are convened to discuss countermeasures. If necessary, a Major Incident Response Meeting is held, and issues are escalated to management, ensuring that all internal departments can respond in a coordinated manner.
In addition, our specialized organization, CSIRT (Computer Security Incident Response Team), collaborates with external security organizations such as Counter Cyber Attack Center, ICT-ISAC, JPCERT/CC (Japan Computer Emergency Response Team Coordination Center), as well as associations including NCA (Nippon CSIRT Association) and FIRST (Forum of Incident Response and Security Teams) to conduct cause investigations and evidence preservation. This ensures control both inside and outside the company toward resolving the incident.
Furthermore, the SSIRT (Service Security Incident Readiness & response Team), which is responsible for services, has established monitoring and reporting systems and collaborates with JPCERT/CC, Council of Anti Phishing Japan, Japan Cybercrime Control Center, and related companies.
Information Security Governance
Information Security Management Cycle
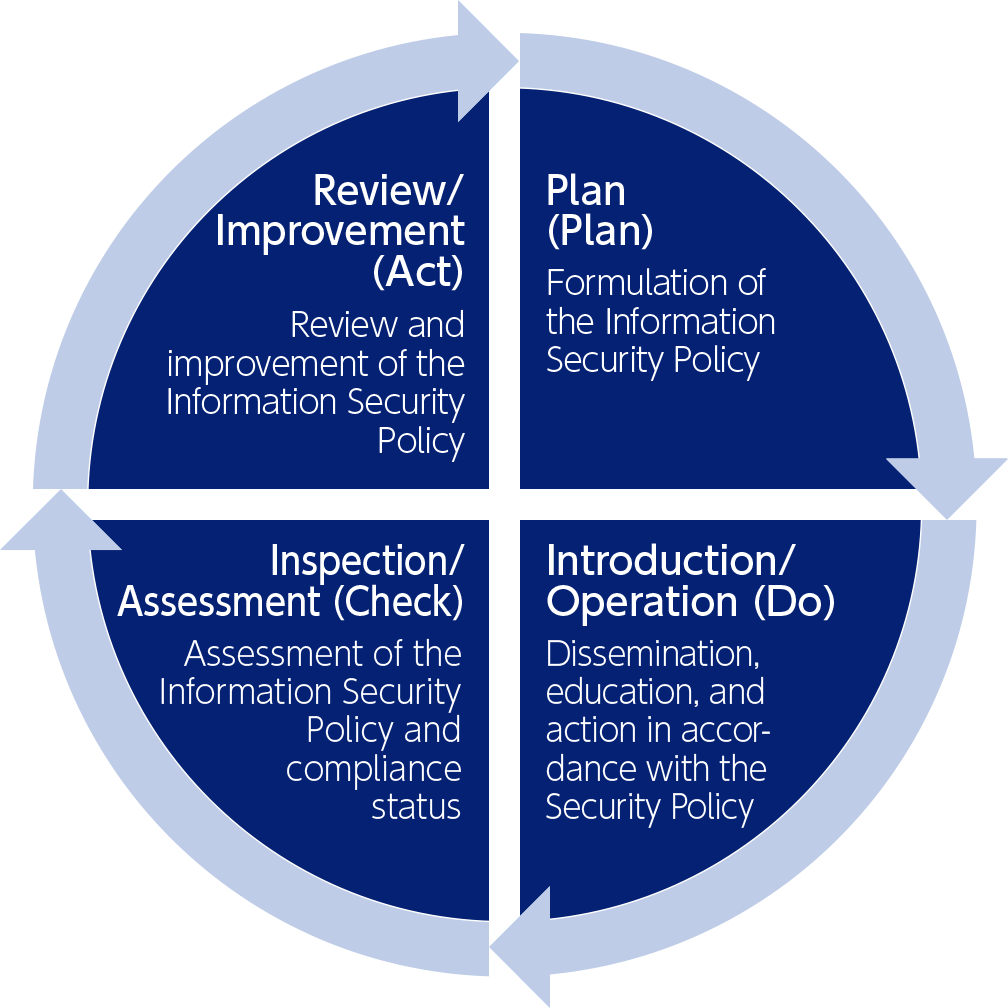
KDDI has obtained ISMS certification (ISO/IEC 27001:2022)* and has introduced an information security management cycle. Under this cycle, KDDI formulates its information security policy at the planning stage and implements checks, reviews, and continuous improvements in accordance with the information security management cycle (the PDCA cycle) described below.
- *A third-party conformity assessment scheme for information security. This scheme aims to contribute to the overall enhancement of information security while achieving an internationally trusted level of information security.
-
-
Plan (Plan)
-
Identify information assets, organize risks and issues, and formulate an Information Security Policy that defines information security measures suited to the organization and company's situation.
-
-
-
Introduction/Operation (Do)
-
Disseminate information to all employees and provide training and other education as necessary. By having employees act in accordance with the Security Policy, we aim to maintain the desired level of information security.
-
-
-
Inspection/Assessment (Check)
-
The Information Security Policy itself will be assessed regularly based on the situation and problems in the field after its introduction, as well as on the social context. Audits are also conducted to ensure compliance.
-
-
-
Review/Improvement (Act)
-
Review and improve the Information Security Policy with reference to the contents of the inspection and assessment.
-
<Overview of the Information Security Management Cycle>
Information Security Audits
ISMS Internal Audits
KDDI conducts internal ISMS audits through in-house auditors for each department and affiliated companies within the scope of its ISMS certification.
These audits verify whether internal information security regulations are being properly implemented, whether information security management activities are being carried out in a planned manner, and whether ISMS activities have been effectively embedded in and are functioning within the audited organizations.
If any nonconformities are identified, corrective actions are required.
In addition, KDDI analyzes the results of the ISMS internal audits and, based on evaluations of their effectiveness, conducts reviews and continuous improvements.
Audits of External Partners
In cases where KDDI outsources part or all of its operations involving KDDI's information assets, it conducts audits of its contractors at least once a year to confirm that a security level equivalent to that of KDDI is appropriately maintained.
In addition, each year KDDI selects certain high-importance outsourced operations and carries out special audits of the contractors by auditors from specialized departments.
Management of Information Assets Based on Their Importance
KDDI classifies information assets based on internal information security regulations, and ensures proper information assets management by implementing security measures according to their level of importance. This ensures appropriate management of information assets. For example, customer information is handled only on devices that are isolated from the internet and subject to strict access control, so that only authorized devices can access these assets. In addition, information assets classified as highly important are protected with strong encryption to prevent access by external parties.
By implementing security measures according to the importance of information assets, KDDI achieves thorough and robust management of its information assets.
Development of Security Personnel
KDDI has established a security human resource development program and is committed to systematic security human resource development to protect customer data and the services we provide from cyberattacks. In this program, we actively encourage the acquisition of the national certification "Registered Information Security Specialist (Cybersecurity Specialist)" operated by the Information-technology Promotion Agency, Japan (IPA). We provide support for certification preparation, including specialized training and learning assistance. As of October 2025, the number of certified individuals within the KDDI Group is 321*, making it one of the largest in the country.
- *Based on the IPA registered names, individuals whose employer is registered as "KDDI Corporation" were extracted (as of October 2025).
Human resource development is a crucial initiative aimed at fostering employee growth and showcasing the high level of a company. KDDI's goal is to enhance expertise and technical capabilities through an increase in certified individuals. Additionally, we conduct e-learning information security training for a target audience of 11,000 employees, continuously working on improving the security awareness and skills of our employees. By continuously learning about the latest cyber threat trends, information leak cases, and their countermeasures, we aim to raise awareness of information security and improve skills to prevent incidents.
| Content | Target | Implementation method |
|---|---|---|
| Security training for new employees | New employees | Group-based training |
| Basic security training | All employees | e-learning |
| Security training for line managers | Line managers | e-learning/Group-based training |
<Example of Information Security Training>
Measures for Enhancing Security
System Security Audits and Vulnerability Assessments
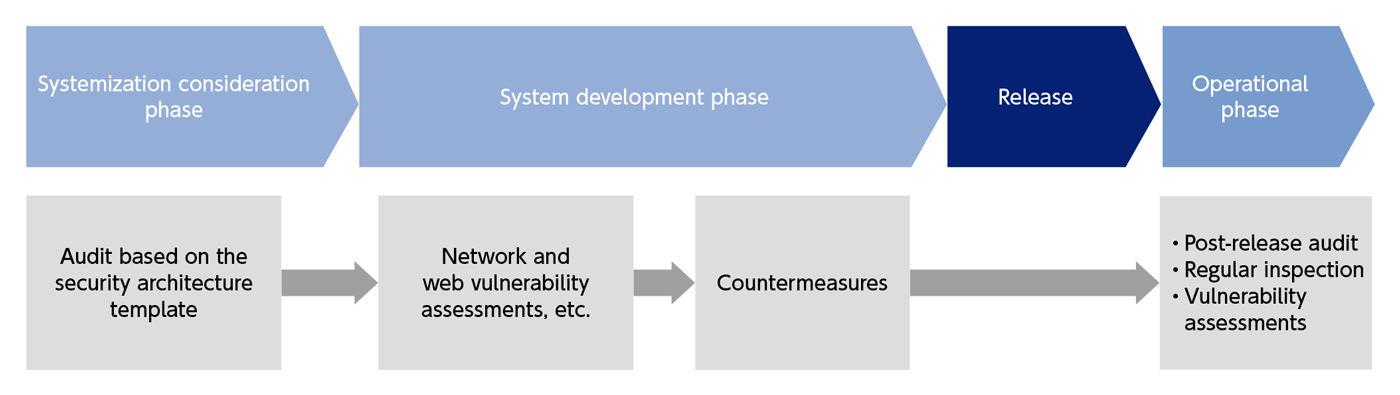
KDDI conducts system security audits through specialized departments to verify compliance with required security requirements when systems are constructed or modified, in accordance with the "Company-Wide System Security Management Guidelines." In these audits, we use a security architecture template that breaks down the security requirements defined in the guidelines into implementation-level details, and confirm compliance with each item during the system planning phase. The guidelines and security architecture templates used in the audits are reviewed and revised as appropriate based on the latest cyberattack methods, and we continuously work to enhance our security level.
In addition to checks conducted during the planning phase using the security architecture template, system security audits also include network and web vulnerability assessments during the development phase to identify vulnerabilities in actual systems. Furthermore, after systems are released, we continue to maintain and strengthen the security level of our systems by conducting regular audits, inspections, and vulnerability assessments during the operational phase.
Security Monitoring
KDDI centrally monitors telecommunications facilities across the country and, in the event of a large-scale outage, coordinates with each site to provide overall command, recovery instructions, and information dissemination. In the unlikely event of a cyberattack, KDDI has established a system that links integrated monitoring with security monitoring, enabling rapid response.
In security monitoring, specially trained security engineers observe threats such as unauthorized access, tampering, and targeted attacks 24 hours a day, 365 days a year. Logs generated by security monitoring devices are continuously analyzed to detect early signs of attacks among vast amounts of data. If a critical incident, such as unauthorized access or tampering, occurs, it is detected in real time, and CSIRT and relevant internal departments are promptly informed and guided on the appropriate response.
To ensure that security monitoring continues even during emergencies, KDDI has established systems and procedures as part of its Business Continuity Plan (BCP). Furthermore, to verify the effectiveness of these systems and procedures, improve proficiency, and implement enhancements, KDDI regularly conducts training exercises based on a variety of simulated scenarios for business continuity.
Service Security Initiatives
Phishing attacks―such as fraudulent emails or SMS messages that redirect users to fake websites to steal authentication credentials―continue to rise. These attacks increasingly involve installing malware through malicious apps. To address such threats, KDDI has established SSIRT (Service Security Incident Readiness & Response Team), a dedicated organization focused on preventing service misuse that could harm customers.
SSIRT implements proactive measures against phishing, including traditional anti-spam efforts, customer alerts, and active detection of fraudulent websites in collaboration with relevant organizations. We also maintain a 24/7 monitoring system to detect and prevent unauthorized logins using compromised accounts. Furthermore, KDDI has introduced expert audits during the service planning process to identify and eliminate authentication weaknesses before launch, reinforcing our security posture.
As phishing techniques grow more sophisticated, KDDI remains vigilant against emerging threats and continues to strengthen service security while implementing countermeasures for new risks.
Cybersecurity Annual Report
We publish the Cyber Security Annual Report with the aim of introducing the KDDI Group's information security activities to our stakeholders and increasing the reliability of our business.
External Security Evaluation
We disclose information on External security evaluations with the aim of presenting to our stakeholders the assessment results by domestic and international evaluation organizations regarding KDDI's information security initiatives, and of enhancing the objectivity of KDDI's security posture as well as the reliability of our business.



